Photo from wikipedia
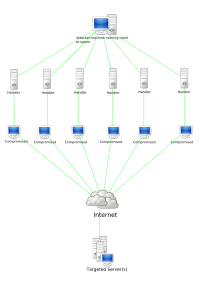
Distributed Denial-of-Service (DDoS) attacks are usually launched through the botnet, an “army” of compromised nodes hidden in the network. Inferential tools for DDoS mitigation should accordingly enable an early and… Click to show full abstract
Distributed Denial-of-Service (DDoS) attacks are usually launched through the botnet, an “army” of compromised nodes hidden in the network. Inferential tools for DDoS mitigation should accordingly enable an early and reliable discrimination of the normal users from the compromised ones. Unfortunately, the recent emergence of attacks performed at the application layer has multiplied the number of possibilities that a botnet can exploit to conceal its malicious activities. New challenges arise, which cannot be addressed by simply borrowing the tools that have been successfully applied so far to earlier DDoS paradigms. In this paper, we offer basically three contributions: 1) we introduce an abstract model for the aforementioned class of attacks, where the botnet emulates normal traffic by continually learning admissible patterns from the environment; 2) we devise an inference algorithm that is shown to provide a consistent (i.e., converging to the true solution as time elapses) estimate of the botnet possibly hidden in the network; and 3) we verify the validity of the proposed inferential strategy on a test-bed environment. Our tests show that, for several scenarios of implementation, the proposed botnet identification algorithm needs an observation time in the order of (or even less than) 1 min to identify correctly almost all bots, without affecting the normal users’ activity.
Journal Title: IEEE Transactions on Information Forensics and Security
Year Published: 2017
Link to full text (if available)
Share on Social Media: Sign Up to like & get
recommendations!