
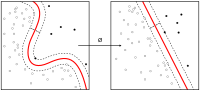
Amorphous Tungsten Oxide Homojunction‐Based Optoelectronic Memristor Array Mimicking Local Image Enhancement for Network Intrusion Detection System
Sign Up to like & getrecommendations! Published in 2025 at "Advanced Functional Materials"
DOI: 10.1002/adfm.202523643
Abstract: The performance of network intrusion detection systems is constrained by factors related to data quality and the richness of feature information. Generic data preprocessing methods often struggle to effectively capture local features, which further diminishes… read more here.
Keywords: detection; enhancement; image; intrusion detection ... See more keywords

Optimizing Intrusion Detection for IoT: A Systematic Review of Machine Learning and Deep Learning Approaches With Feature Selection and Data Balancing
Sign Up to like & getrecommendations! Published in 2025 at "Wiley Interdisciplinary Reviews: Data Mining and Knowledge Discovery"
DOI: 10.1002/widm.70008
Abstract: As the Internet of Things (IoT) continues expanding its footprint across various sectors, robust security systems to mitigate associated risks are more critical than ever. Intrusion Detection Systems (IDS) are fundamental in safeguarding IoT infrastructures… read more here.
Keywords: review; systematic review; intrusion detection; machine learning ... See more keywords

Review of intrusion detection systems based on deep learning techniques: coherent taxonomy, challenges, motivations, recommendations, substantial analysis and future directions
Sign Up to like & getrecommendations! Published in 2019 at "Neural Computing and Applications"
DOI: 10.1007/s00521-019-04557-3
Abstract: This study reviews and analyses the research landscape for intrusion detection systems (IDSs) based on deep learning (DL) techniques into a coherent taxonomy and identifies the gap in this pivotal research area. The focus is… read more here.
Keywords: analysis; deep learning; detection systems; intrusion detection ... See more keywords
A stacked ensemble learning model for intrusion detection in wireless network
Sign Up to like & getrecommendations! Published in 2020 at "Neural Computing and Applications"
DOI: 10.1007/s00521-020-04986-5
Abstract: Intrusion detection pretended to be a major technique for revealing the attacks and guarantee the security on the network. As the data increases tremendously every year on the Internet, a single algorithm is not sufficient… read more here.
Keywords: ensemble learning; intrusion detection; network; stacked ensemble ... See more keywords

Contextual information fusion for intrusion detection: a survey and taxonomy
Sign Up to like & getrecommendations! Published in 2017 at "Knowledge and Information Systems"
DOI: 10.1007/s10115-017-1027-3
Abstract: Research in cyber-security has demonstrated that dealing with cyber-attacks is by no means an easy task. One particular limitation of existing research originates from the uncertainty of information that is gathered to discover attacks. This… read more here.
Keywords: contextual information; intrusion detection; information; survey ... See more keywords

Using homomorphic encryption for privacy-preserving clustering of intrusion detection alerts
Sign Up to like & getrecommendations! Published in 2020 at "International Journal of Information Security"
DOI: 10.1007/s10207-020-00506-7
Abstract: Cyber-security attacks are becoming more frequent and more severe day by day. To detect the execution of such attacks, organizations install intrusion detection systems. It would be beneficial for such organizations to collaborate, to better… read more here.
Keywords: detection; privacy preserving; intrusion detection; detection alerts ... See more keywords

MLSTL-WSN: machine learning-based intrusion detection using SMOTETomek in WSNs
Sign Up to like & getrecommendations! Published in 2024 at "International Journal of Information Security"
DOI: 10.1007/s10207-024-00833-z
Abstract: In the domain of cyber-physical systems, wireless sensor networks (WSNs) play a pivotal role as infrastructures, encompassing both stationary and mobile sensors. These sensors self-organize and establish multi-hop connections for communication, collectively sensing, gathering, processing,… read more here.
Keywords: detection; intrusion detection; wsns; machine learning ... See more keywords

A comprehensive and systematic literature review on intrusion detection systems in the internet of medical things: current status, challenges, and opportunities
Sign Up to like & getrecommendations! Published in 2025 at "Artificial Intelligence Review"
DOI: 10.1007/s10462-024-11101-w
Abstract: The increasing number of medical devices in the Internet of Medical Things (IoMT) environment has raised significant cybersecurity concerns. These devices often have weak security features, poor design, and insufficient authentication protocols, making them vulnerable… read more here.
Keywords: intrusion detection; intrusion; paper; security ... See more keywords

An intrusion detection approach based on improved deep belief network
Sign Up to like & getrecommendations! Published in 2020 at "Applied Intelligence"
DOI: 10.1007/s10489-020-01694-4
Abstract: In today’s interconnected society, cyberattacks have become more frequent and sophisticated, and existing intrusion detection systems may not be adequate in the complex cyberthreat landscape. For instance, existing intrusion detection systems may have overfitting, low… read more here.
Keywords: approach based; network; intrusion; intrusion detection ... See more keywords

Advanced IDS: a comparative study of datasets and machine learning algorithms for network flow-based intrusion detection systems
Sign Up to like & getrecommendations! Published in 2025 at "Applied Intelligence"
DOI: 10.1007/s10489-025-06422-4
Abstract: Globally, cyberattacks are growing and mutating each month. Intelligent Intrusion Network Detection Systems are developed to analyze and detect anomalous traffic to face these threats. A way to address this is by using network flows,… read more here.
Keywords: detection; algorithms network; intrusion detection; network flow ... See more keywords

Multi-level trust based intelligence intrusion detection system to detect the malicious nodes using elliptic curve cryptography in MANET
Sign Up to like & getrecommendations! Published in 2017 at "Cluster Computing"
DOI: 10.1007/s10586-017-0927-z
Abstract: Mobile ad hoc networks (MANETs) are qualified by multi-hop wireless links and resource restrained nodes. Generally, mobile ad hoc networks (MANETs) are susceptible to various attacks like gray hole attack, black hole attack, selective packet… read more here.
Keywords: attack; detection system; detection; trust ... See more keywords