
The application of a novel neural network in the detection of phishing websites
Sign Up to like & getrecommendations! Published in 2018 at "Journal of Ambient Intelligence and Humanized Computing"
DOI: 10.1007/s12652-018-0786-3
Abstract: In recent years, security incidents of website occur increasingly frequently, and this motivates us to study websites’ security. Although there are many phishing detection approaches to detect phishing websites, the detection accuracy has not been… read more here.
Keywords: phishing detection; detection; detection model; phishing websites ... See more keywords

Phishing detection on webpages in European non-English languages based on machine learning
Sign Up to like & getrecommendations! Published in 2025 at "Scientific Reports"
DOI: 10.1038/s41598-025-21384-w
Abstract: Machine learning-based phishing detection is crucial for preventing zero-day attacks. State-of-the-art phishing detection performs well on English webpages. However, it is not adequately accurate for webpages in minor languages. This work significantly improves phishing detection… read more here.
Keywords: detection; minor languages; machine learning; language ... See more keywords
Exquisite Analysis of Popular Machine Learning–Based Phishing Detection Techniques for Cyber Systems
Sign Up to like & getrecommendations! Published in 2020 at "Journal of Applied Security Research"
DOI: 10.1080/19361610.2020.1816440
Abstract: Abstract Recent advances in data science have made available many URL-analysis–based detection and machine learning algorithms, which are being leveraged for phishing detection. It is necessary to measure the efficacy of each technique so as… read more here.
Keywords: phishing detection; detection; machine learning; analysis ... See more keywords

The Answer is in the Text: Multi-Stage Methods for Phishing Detection Based on Feature Engineering
Sign Up to like & getrecommendations! Published in 2020 at "IEEE Access"
DOI: 10.1109/access.2020.3043396
Abstract: A phishing attack is a threat based on fraudulent communication, usually by e-mail, where the cybercriminals, impersonating a trusted person or organization, try to lure and coax a target. Phishing detection approaches that obtain highly… read more here.
Keywords: phishing detection; feature engineering; stage; multi stage ... See more keywords

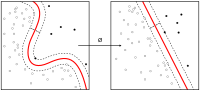
PDGAN: Phishing Detection With Generative Adversarial Networks
Sign Up to like & getrecommendations! Published in 2022 at "IEEE Access"
DOI: 10.1109/access.2022.3168235
Abstract: Phishing is a harmful online attack that could lead to identity theft and financial damages. The demand for high-accuracy phishing detection tools has risen due to the increase of online electronic services and payment systems.… read more here.
Keywords: network; accuracy; generative adversarial; phishing detection ... See more keywords

Phishing Detection System Through Hybrid Machine Learning Based on URL
Sign Up to like & getrecommendations! Published in 2023 at "IEEE Access"
DOI: 10.1109/access.2023.3252366
Abstract: Currently, numerous types of cybercrime are organized through the internet. Hence, this study mainly focuses on phishing attacks. Although phishing was first used in 1996, it has become the most severe and dangerous cybercrime on… read more here.
Keywords: machine; machine learning; system hybrid; detection system ... See more keywords

Multimodal Phishing Detection on Social Networking Sites: A Systematic Review
Sign Up to like & getrecommendations! Published in 2025 at "IEEE Access"
DOI: 10.1109/access.2025.3579584
Abstract: Phishing is one of the most common cyberattacks, with the number of incidents increasing annually. Significant research interests have been generated in phishing emails, URLs, and websites over the past decade. Phishing attackers often target… read more here.
Keywords: systematic review; multimodal phishing; phishing detection; networking sites ... See more keywords

Enhanced Voice Phishing Detection Using an LLM-Based Framework for Data Augmentation and Classification
Sign Up to like & getrecommendations! Published in 2025 at "IEEE Access"
DOI: 10.1109/access.2025.3603007
Abstract: Existing voice phishing detection models based on call transcripts often suffer from limited generalizability due to insufficient scenario diversity and the absence of ambiguous samples in data. To address these challenges, we propose an integrated… read more here.
Keywords: detection; call transcripts; framework; phishing detection ... See more keywords

Privacy-Preserving Federated Learning for Phishing Detection
Sign Up to like & getrecommendations! Published in 2025 at "IEEE Technology and Society Magazine"
DOI: 10.1109/mts.2025.3558971
Abstract: Machine learning is one of the most prominent technologies used to combat phishing detection; however, the vast amount of data required for training models for detection raises a privacy concern for end users. Gathering email… read more here.
Keywords: privacy; machine learning; federated learning; learning phishing ... See more keywords

Phishing Detection on Ethereum via Attributed Ego-Graph Embedding
Sign Up to like & getrecommendations! Published in 2022 at "IEEE Transactions on Circuits and Systems II: Express Briefs"
DOI: 10.1109/tcsii.2022.3159594
Abstract: In recent years, the losses caused by phishing scams on Ethereum have reached a level that cannot be ignored. In such a phishing detection scenario, network embedding is seen as an effective solution. In this… read more here.
Keywords: transaction; phishing detection; ego graph; ethereum ... See more keywords

Unraveling the Deception of Web3 Phishing Scams: Dynamic Multiperspective Cascade Graph Approach for Ethereum Phishing Detection
Sign Up to like & getrecommendations! Published in 2025 at "IEEE Transactions on Computational Social Systems"
DOI: 10.1109/tcss.2024.3516144
Abstract: Ethereum, as one of the most active cryptocurrency trading platforms, has garnered significant academic interest due to its transparent and accessible transaction data. In recent years, phishing scams have emerged as a serious criminal activity… read more here.
Keywords: transaction; phishing scams; ethereum; network ... See more keywords